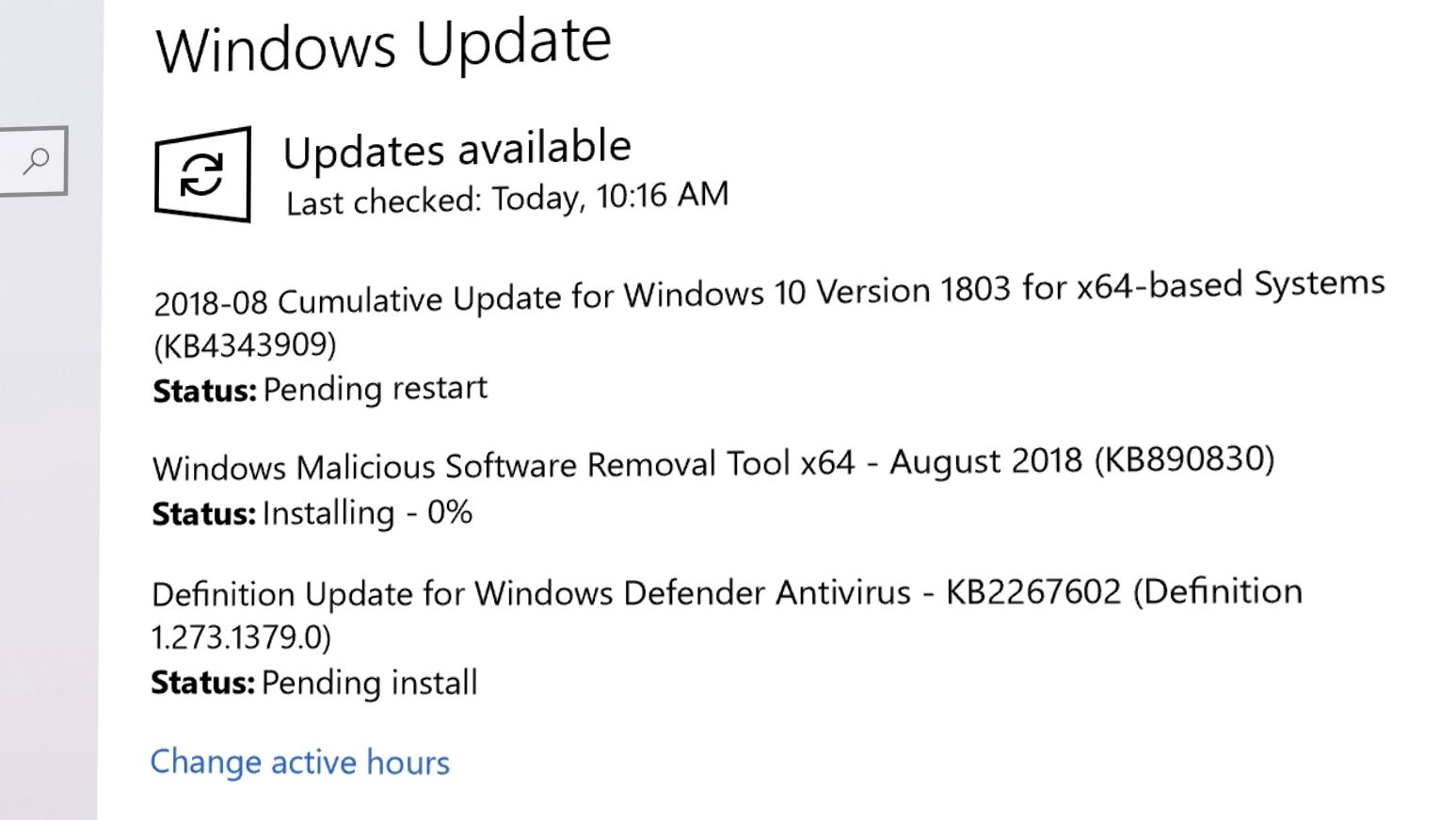
Microsoft har lansert oppdateringen KB4343909 til Windows 10 1803.
Oppdatert, 23:08:
Intel har nå kommentert og dermed bekreftet den nye feilen som er rettet i denne oppdateringen, kalt L1 Terminal Fault.
Disse Core og Xeon-produktene er berørte.
Annonse
Oppdatert,
Dette er rettet:
- Provides protections against a new speculative execution side-channel vulnerability known as L1 Terminal Fault (L1TF) that affects Intel® Core® processors and Intel® Xeon® processors (CVE-2018-3620 and CVE-2018-3646). Make sure previous OS protections against Spectre Variant 2 and Meltdown vulnerabilities are enabled using the registry settings outlined in the Windows Client and Windows Server guidance KB articles. (These registry settings are enabled by default for Windows Client OS editions, but disabled by default for Windows Server OS editions.)
- Addresses an issue that causes high CPU usage that results in performance degradation on some systems with Family 15h and 16h AMD processors. This issue occurs after installing the June 2018 or July 2018 Windows updates from Microsoft and the AMD microcode updates that address Spectre Variant 2 (CVE-2017-5715 – Branch Target Injection).
- Addresses an issue that prevents apps from receiving mesh updates after resuming. This issue occurs for apps that use Spatial Mapping mesh data and participate in the Sleep or Resume cycle.
- Ensures that Internet Explorer and Microsoft Edge support the preload=»none» tag.
- Addresses an issue that prevents some applications running on HoloLens, such as Remote Assistance, from authenticating after upgrading from Windows 10, version 1607, to Windows 10, version 1803.
- Addresses an issue that significantly reduced battery life after upgrading to Windows 10, version 1803.
- Addresses an issue that causes Device Guard to block some ieframe.dll class IDs after installing the May 2018 Cumulative Update.
- Addresses a vulnerability related to the Export-Modulemember() function when used with a wildcard (*) and a dot-sourcing script. After installing this update, existing modules on devices that have Device Guard enabled will intentionally fail. The exception error is “This module uses the dot-source operator while exporting functions using wildcard characters, and this is disallowed when the system is under application verification enforcement.” For more information, see https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/CVE-2018-8200 and https://aka.ms/PSModuleFunctionExport.
- Security updates to Windows Server.
Kilde:
Microsoft
Lansert til Windows 10: slik bruker du Your Phone i Windows 10
Last ned den nyeste oppdateringen
1803 er den siste stabile versjonen som er en del av Redstone 4. Redstone 5 er for tiden under beta-testing, men er nærme en lansering i høst.
Det er foreløpig ikke avslørt hva som er nytt i KB4343909, men vi oppdaterer denne artikkelen når vi vet mer.